A Step-by-Step Guide for Policymakers: Tackling Online Harm While Preserving the Open Internet
Introduction
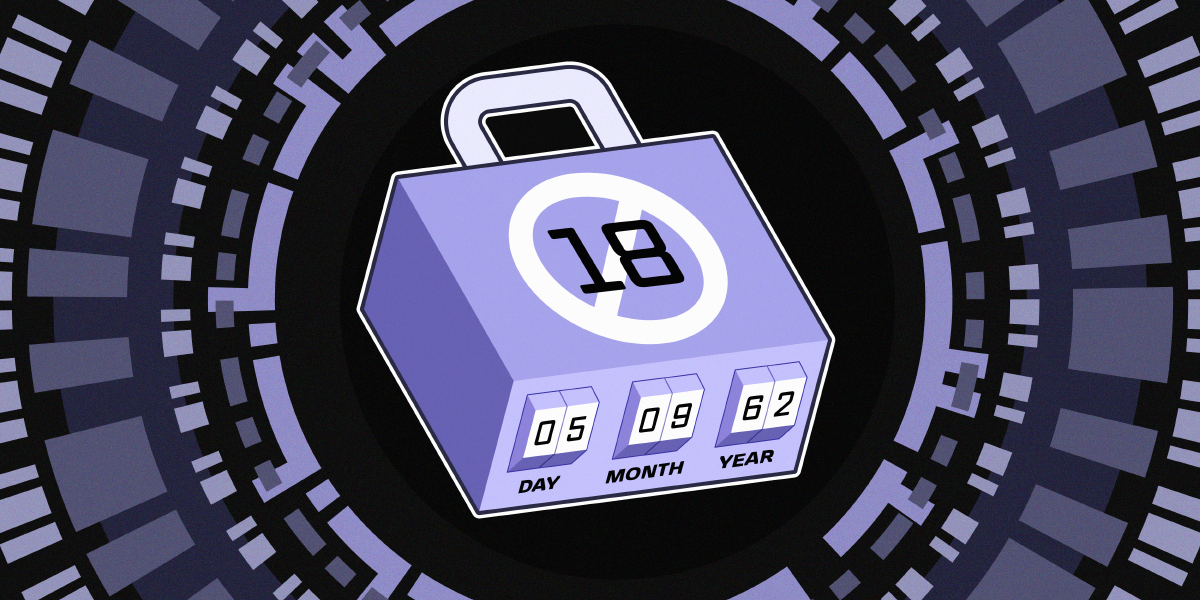
When the Electronic Frontier Foundation (EFF) and 18 organizations—including Mozilla, the Tor Project, and Open Rights Group—wrote to UK policymakers, they delivered a clear warning: heavy-handed restrictions like sweeping age-gating and access controls risk dismantling the open web without addressing the true drivers of online harm. This guide translates their core message into actionable steps for legislators, regulators, and advocates who want to protect users—especially children—without sacrificing privacy, anonymity, or the internet’s fundamental architecture. By focusing on root causes and rights-respecting design, you can craft policies that reduce harm while keeping the web a global public resource.
What You Need
- Understanding of the policy landscape: Familiarity with the UK’s Children’s Wellbeing and Schools Bill and related proposals.
- Knowledge of age assurance technologies: Awareness of their privacy-invasive and accuracy limitations.
- Coalition-building skills: Ability to engage civil society, tech companies, and human rights experts.
- Commitment to evidence-based policymaking: Willingness to prioritize data over quick fixes.
- Access to research: Studies on platform design, surveillance capitalism, and online youth experiences.
Step-by-Step Guide
Step 1: Identify the Root Causes of Online Harm
Before writing any regulation, analyze what actually drives harm. The coalition’s letter points to business models built on pervasive data collection and targeted advertising. Platforms design features to maximize engagement—often at the expense of safety and autonomy. Start by mapping how algorithmic amplification, dark patterns, and lack of transparency contribute to issues like cyberbullying, misinformation, and exploitation. Hold workshops with academics and child safety experts to separate symptoms from causes.
Step 2: Avoid Blanket Age-Gating and Access Restrictions
Proposed measures often require all users to verify identity via age assurance technologies before accessing services—from social media and video games to VPNs and simple websites. This is a blunt tool. As the letter warns, these systems are either inaccurate (falsely blocking legitimate users) or privacy-invasive (collecting sensitive data). Worse, they undermine anonymity and create surveillance risks. Instead, reject any mandate that forces identity checks on the entire user base. If age verification is considered, limit it to specific, high-risk services and ensure it is voluntary, transparent, and privacy-protecting.
Step 3: Prioritize Rights-Respecting Alternatives
Rather than restricting access, design policies that empower users. Require platforms to integrate safety features by default—like complaint mechanisms, robust reporting tools, and privacy-by-design architecture. Encourage the development of age-appropriate experiences without compulsory identity checks. For example, offer “safe modes” that filter content based on context, not user age. The internet must remain accessible to all, especially young people who rely on it for information, support, and expression that may not exist offline.
Step 4: Hold Companies Accountable for Systemic Practices
The coalition’s message: target the business model, not the user. Introduce mandatory transparency reports on data collection, advertising targeting, and algorithmic decision-making. Impose fines for practices that prioritize engagement over safety, such as using dark patterns to lure children into addictive loops. Require independent audits of platform design for high-risk services. Accountability must shift from individual behavior to corporate responsibility.

Step 5: Preserve the Core Architecture of the Open Web
Blunt restrictions fragment the internet into jurisdictional silos, empower gatekeepers (like app stores), and limit interoperability. As the letter notes, age-gating at scale erodes openness and accessibility. Guard against this by including “internet freedom” clauses in any regulation. Ensure that new rules do not inadvertently require technologies that break end-to-end encryption or force all traffic through centralized identity providers. Maintain the web as a global public resource where anyone can participate without prior permission.
Step 6: Engage Diverse Stakeholders
Policymaking should not happen in isolation. Follow the coalition’s example: bring together civil liberty groups, technology nonprofits, child rights advocates, and industry representatives. Public consultation ensures that policies reflect a wide range of expertise and avoid unintended consequences. Create an advisory panel that includes privacy experts and youth representatives. Use their input to refine proposals before they become law.
Step 7: Protect Young People’s Access to Vital Online Resources
Remember that the internet is a lifeline for many youths—offering educational content, mental health support, and communities of peers with similar experiences. Restrictive policies risk cutting off these benefits without meaningfully reducing harm. As you craft solutions, explicitly assess their impact on young people’s right to access information and free expression. Include a provision that any measure must demonstrate a net positive effect for youth well-being, not just a reduction in easily measurable categories of risk.
Tips for Success
- Focus on outcomes over appearances: A policy that looks tough on tech but fails to reduce harm is counterproductive. Measure success by actual safety improvements, not by the number of age gates deployed.
- Don't rush: Rapid implementations often rely on immature technologies. Give the industry time to develop privacy-friendly solutions.
- International coordination: Online harm is borderless. Align with efforts in other jurisdictions (e.g., EU’s Digital Services Act) to avoid fragmented enforcement.
- Public education: Help citizens understand why privacy and anonymity matter. Build support for policies that prioritize rights.
- Iterate based on feedback: After initial implementation, review and adjust. The internet changes fast—your policy must adapt too.
Related Articles
- Go 1.26 Launches Revamped 'go fix' to Automate Code Modernization
- Developers Unveil 39 AI Projects at JetBrains Codex Hackathon, Top Prize Goes to 'Hyperreasoning' Agent
- Top 10 GSoC 2026 Projects: AI and Beyond
- 10 Key Insights into the Lomiri Tech Meeting: A Free Open Source Mobile Dev Hackathon in the Netherlands
- Securing Your Autonomous AI Agent: A Practical Guide to Safely Deploying Tools Like OpenClaw
- Enhance Your Python Projects with Codex CLI: A Comprehensive Guide
- Mastering Jakarta EE: A Comprehensive Guide to Enterprise Java
- Mastering Java Lists: Essential Operations and Best Practices