Frontier AI and the Evolution of Cyber Defense: A Q&A
In recent developments, frontier AI models from labs like OpenAI and Anthropic are accelerating the transformation of cybersecurity. SentinelOne, a leader in AI-native defense, has long partnered with these labs to integrate advanced capabilities into its platform. This Q&A explores how frontier AI is reshaping threat detection, the balance between attacker and defender advantages, and the practical implications for modern security operations.
What is frontier AI and how is it influencing modern cybersecurity?
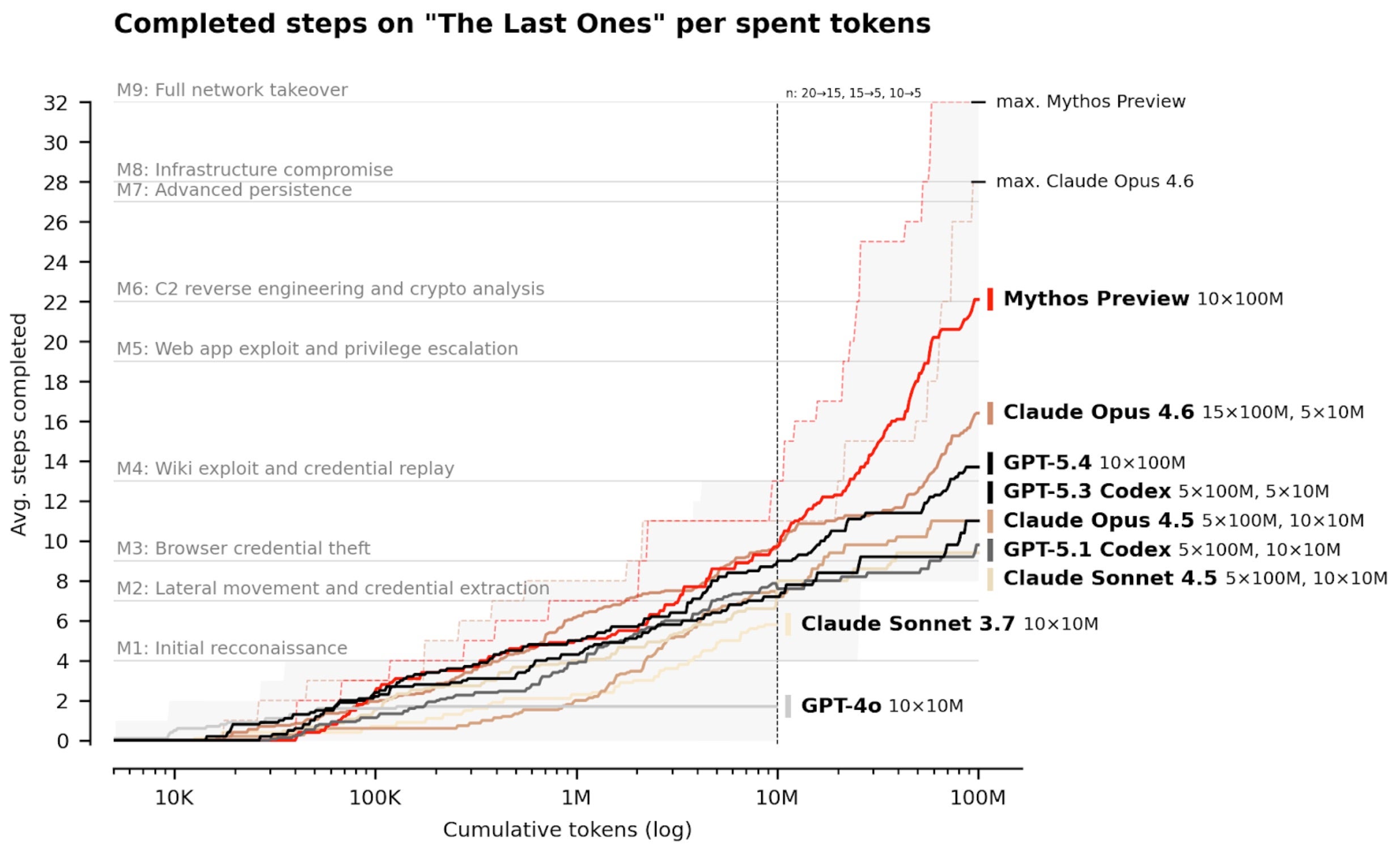
Frontier AI refers to the most advanced generative models, such as those developed by OpenAI, Anthropic, and Google DeepMind. These models are increasingly capable of reasoning about complex systems, identifying vulnerabilities, and automating security workflows. For defenders, this means faster analysis of attack paths and improved detection of novel threats. However, attackers can also leverage these models to scale vulnerability discovery and exploit development. The race between offense and defense is accelerating, but the real value lies in operational resilience—understanding which vulnerabilities pose actual risk in live environments, rather than just counting exposures. SentinelOne has embedded insights from these partnerships into its platform, enabling real-time autonomous responses that reduce the window of exploitation.
How does SentinelOne collaborate with frontier AI labs to enhance its platform?
SentinelOne has maintained ongoing collaborations with leading frontier labs, including OpenAI, Anthropic, and Google DeepMind, for several years. While specific details of every collaboration remain confidential, these partnerships provide invaluable insight into the evolution of advanced models and their practical applications in security. Some of these learnings are already integrated into SentinelOne's platform, improving behavioral AI, automation, and autonomous protection. For instance, the company uses insights from frontier models to enhance reasoning about attack paths and to develop faster response mechanisms. These collaborations help SentinelOne stay ahead of emerging threats, such as zero-day exploits that no other solution can currently stop. The knowledge transfer allows the platform to operate more intelligently across endpoint, cloud, and identity layers, ultimately delivering greater protection to customers.
What advantages do frontier AI models offer to both cyber defenders and attackers?
Frontier AI models provide asymmetric advantages. For defenders, they enable quicker identification of system weaknesses, automated analysis of complex architectures, and smarter prioritization of remediation efforts. They can simulate attack scenarios and generate defensive strategies at machine speed. For attackers, however, these models also lower the barrier to discovering vulnerabilities—they can exploit code analysis and generate exploit payloads faster than ever before. This dual-use nature creates a continuous pressure on security teams. The key differentiator is not just finding more vulnerabilities but understanding which ones are exploitable in real-world environments and having automated responses ready. SentinelOne's AI-native approach focuses on that gap, using contextual awareness and runtime protections to filter out theoretical risks and stop actual attacks, even those leveraging zero-day flaws.
Why is the gap between theoretical vulnerability discovery and actual risk important?
Not all discovered vulnerabilities translate into real-world threats. Many are mitigated by existing controls, architectural layers, or runtime protections. For example, a buffer overflow in a non‑networked component may pose no immediate risk. Focusing solely on raw vulnerability counts can lead to wasted effort and alert fatigue. Understanding the actual exploitability under operational conditions is crucial. Frontier AI can help bridge this gap by simulating attack scenarios and assessing contextual factors, but it also amplifies the noise of theoretical risks if used without proper filtering. SentinelOne’s platform emphasizes behavioral AI that monitors runtime activity and correlates threats with environmental context, automatically blocking only those attempts that pose genuine danger. This approach ensures that security teams concentrate on what matters most: stopping actual attacks, including novel threats and zero-days, rather than chasing irrelevant exposures.
How does SentinelOne’s platform achieve autonomous response at machine speed?
From its inception, SentinelOne was built to operate at machine speed using behavioral AI and automation. The platform continuously monitors activity across endpoints, cloud workloads, identities, networks, and AI pipelines. When it detects malicious behavior—such as an unexpected process spawning or data exfiltration attempt—it can respond autonomously in real time. This includes terminating processes, isolating devices, or rolling back changes without human intervention. The integration with frontier AI insights further refines detection models, enabling the system to recognize novel attack patterns even without known signatures. Recent examples include blocking supply chain attacks like LiteLLM, Axios, and CPU-Z, where unpatched zero-day vulnerabilities were exploited. Autonomous response at machine speed was the only effective countermeasure, as manual analysis would have been too slow to prevent damage.
What recent supply chain attacks demonstrate the need for AI-native defense?
In the past few weeks alone, supply chain attacks on LiteLLM, Axios, and CPU-Z have highlighted the critical role of autonomous response. These attacks exploited zero-day vulnerabilities and abused trusted agents and workflows in the AI era. In each case, the attack vector was novel and unpatched—traditional signature-based defenses failed. Only an AI-native platform capable of behavioral analysis and automatic remediation could block these threats at machine speed. The attacks illustrate how adversaries increasingly target the software supply chain, leveraging legitimate tools and processes to bypass conventional security measures. SentinelOne’s platform, by operating autonomously and using behavioral AI, detected the malicious deviations from normal behavior and responded immediately, containing the attack before it could spread. This demonstrates the necessity of AI-native defense in a landscape where attackers move fast and exploit trust.
What is the future of AI-native defense in cybersecurity?
As frontier AI models continue to advance, AI-native defense will become essential. The ability to process massive data streams, reason about complex attack paths, and respond autonomously at machine speed is no longer optional—it is a fundamental requirement. Future defenses will likely rely even more on contextual awareness, predictive analytics, and continuous adaptation. SentinelOne’s pioneering principle—building from day one with behavioral AI and automation—positions it well for this future. The company will continue to partner with frontier labs to integrate cutting-edge capabilities, ensuring that its platform evolves faster than threats. The ultimate goal remains: to reduce the gap between theoretical exposure and operational risk, and to stop attacks automatically, even as adversaries leverage the same AI advances to develop more sophisticated techniques.
Related Articles
- Senior Scattered Spider Hacker Pleads Guilty in Major Cyber Fraud Case
- AI-Powered Security Sweep Uncovers 271 Zero-Day Vulnerabilities in Firefox
- Security Firms Checkmarx and Bitwarden Targeted in Sophisticated Supply-Chain Attacks
- Canvas Outage During Finals: Cyberattack Disrupts Thousands of Schools
- 10 Critical Facts About the GitHub RCE Bug That Exposed Millions
- Supply Chain Attacks Compromise PyTorch Lightning and Intercom-client: Credential Theft Campaign Revealed
- Understanding Session Timeouts: An Overlooked Accessibility Barrier in Authentication
- Python Releases Urgent Patches: Version 3.14.2 and 3.13.11 Address Regressions and Security Flaws